Answer Brief
Taiwan’s TWCERT/CC issued an urgent alert citing SecurityScorecard’s STRIKE team research into “Operation WrtHug,” a sustained campaign targeting ASUS small office/home office routers worldwide. The activity is reported to abuse known, publicly disclosed OS command-injection vulnerabilities—including issues referenced alongside CVE-2023-39780—focused on the AiCloud service. TWCERT/CC says compromised routers may be backdoored and incorporated into a large global infected network used for follow-on cyber threat activity and espionage, with STRIKE reporting identification of more than 50,000 infected IP devices over the past six months. The advisory urges immediate firmware updates, replacement of end-of-life (EoL) models that cannot be patched, and consultation of ASUS product security advisories for official mitigation steps.
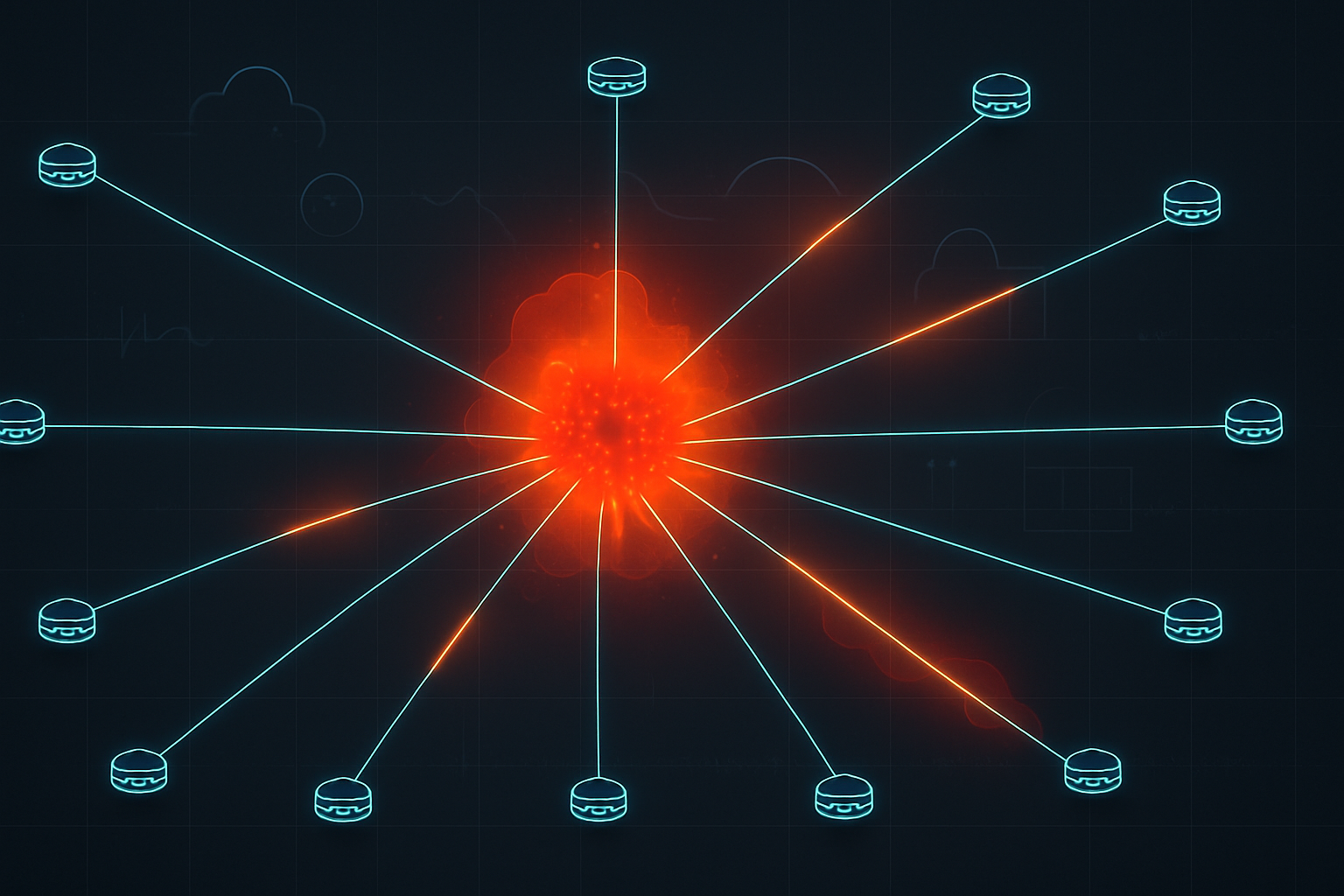
Executive Summary: Taiwan’s TWCERT/CC issued an urgent alert citing SecurityScorecard’s STRIKE team research into “Operation WrtHug,” a sustained campaign targeting ASUS small office/home office routers worldwide. The activity is reported to abuse known, publicly disclosed OS command-injection vulnerabilities—including issues referenced alongside CVE-2023-39780—focused on the AiCloud service. TWCERT/CC says compromised routers may be backdoored and incorporated into a large global infected network used for follow-on cyber threat activity and espionage, with STRIKE reporting identification of more than 50,000 infected IP devices over the past six months. The advisory urges immediate firmware updates, replacement of end-of-life (EoL) models that cannot be patched, and consultation of ASUS product security advisories for official mitigation steps.
Why It Matters
This TWCERT/CC alert matters beyond Taiwan because ASUS routers are widely deployed globally at the network edge—in homes, small offices, remote-worker setups, and branch locations—where compromise can provide durable footholds outside traditional endpoint controls. The advisory frames “Operation WrtHug” as a sustained operation that turns vulnerable routers into infrastructure for further malicious activity and espionage, raising risk not only to consumers but also to enterprises whose employees or vendors rely on unmanaged SOHO networking gear.
The technical signal emphasized by TWCERT/CC is operationally significant: the campaign reportedly leverages publicly known vulnerabilities with available patches, with attackers focusing on the AiCloud service and using OS command-injection as the initial access method (including vulnerabilities associated with CVE-2023-39780). In practice, this highlights two recurring infrastructure risk drivers for defenders: (1) exposed management or value-add services on edge devices (such as cloud/remote access features) and (2) the long tail of end-of-life routers that cannot receive security updates.
For cloud security and identity teams, router-level compromise can become a precursor to downstream account takeover and SaaS abuse (for example, by enabling traffic interception or credential capture), even if cloud platforms are well secured; TWCERT/CC’s warning reinforces why edge-device hygiene is part of modern identity and zero-trust posture. For infrastructure and SOC teams, the report’s emphasis on backdooring and enrolling devices into a global infected network suggests potential for secondary impacts such as scanning, proxying, or acting as staging infrastructure—risks that can manifest as anomalous outbound traffic from small sites and remote offices.
TWCERT/CC’s recommended actions are straightforward and aligned with the stated attack path: update firmware to the latest version, replace EoL devices that cannot be patched, and follow ASUS’s official product security advisory guidance for the vulnerabilities involved. While the alert lists eight specific ASUS router models observed to be affected/targeted, the broader takeaway is that any similar configurations (notably AiCloud exposure and lagging firmware) may increase susceptibility, making asset inventory and lifecycle management of edge networking gear a continuing control gap for many organizations.
Event Type: security
Importance: high
Affected Companies
- ASUS
- SecurityScorecard
Affected Sectors
- Consumer electronics
- Critical infrastructure (indirect exposure)
- Cybersecurity
- Networking
- SOHO/SMB IT
Key Numbers
- ASUS router models listed as impacted/targeted in the alert: 8
- Infected IP devices identified globally (STRIKE claim): >50,000
- Observation window referenced by STRIKE: Past 6 months
- TWCERT/CC publication date: 2025-11-25
Timeline
- SecurityScorecard STRIKE reports identifying more than 50,000 infected IP devices associated with the campaign.
- TWCERT/CC publishes an urgent alert warning ASUS router users to update firmware and review official guidance.