Answer Brief
Taiwan’s national CERT (TWCERT/CC) warns that attackers are increasingly using public blockchains as command-and-control (C2) infrastructure. The advisory highlights “EtherHide,” a technique first described by security researchers in October 2023, where adversaries store malicious commands or payload locations inside smart contracts. Malware (or malicious web scripts) can then query the chain for updated instructions, reducing the effectiveness of traditional controls like domain/IP blocking and traffic monitoring. TWCERT/CC also notes EtherHide is frequently chained with the “ClearFake” social-engineering pattern—fake system notifications or software update prompts—often delivered via compromised WordPress sites embedding malicious JavaScript. The combined flow uses Binance Smart Chain (BSC) smart contracts and read-only calls (e.g., eth_call) to retrieve attacker instructions without on-chain transaction fees, improving stealth and persistence.
Executive Summary: Taiwan’s national CERT (TWCERT/CC) warns that attackers are increasingly using public blockchains as command-and-control (C2) infrastructure. The advisory highlights “EtherHide,” a technique first described by security researchers in October 2023, where adversaries store malicious commands or payload locations inside smart contracts. Malware (or malicious web scripts) can then query the chain for updated instructions, reducing the effectiveness of traditional controls like domain/IP blocking and traffic monitoring. TWCERT/CC also notes EtherHide is frequently chained with the “ClearFake” social-engineering pattern—fake system notifications or software update prompts—often delivered via compromised WordPress sites embedding malicious JavaScript. The combined flow uses Binance Smart Chain (BSC) smart contracts and read-only calls (e.g., eth_call) to retrieve attacker instructions without on-chain transaction fees, improving stealth and persistence.
Why It Matters
Why this matters beyond Taiwan
TWCERT/CC’s write-up is a useful regional signal because it frames a broader, global shift: adversaries testing “Web3-native” infrastructure to make C2 harder to disrupt with the familiar Web2 playbook (domain seizures, IP blocks, sinkholing, and perimeter traffic analytics). If attackers can place live instructions or pointers inside a public chain’s smart contracts, defenders face an asymmetric problem: the data is broadly replicated, difficult to remove, and accessible from many endpoints.
What EtherHide changes in the defender’s equation
According to TWCERT/CC, EtherHide stores either (1) attacker commands or (2) locations of payloads inside smart contracts. That means:
– Network-blocking controls weaken: retrieving instructions can look like ordinary blockchain RPC traffic rather than a connection to a suspicious C2 domain.
– Takedown is structurally difficult: TWCERT/CC emphasizes blockchain immutability—once deployed, the malicious data cannot simply be “taken down” like a server.
– Endpoint and web-layer telemetry becomes more important: the decisive malicious action often happens on the endpoint after a user click, or in the browser via injected JavaScript.
The ClearFake + EtherHide chain: web compromise meets chain-based instruction delivery
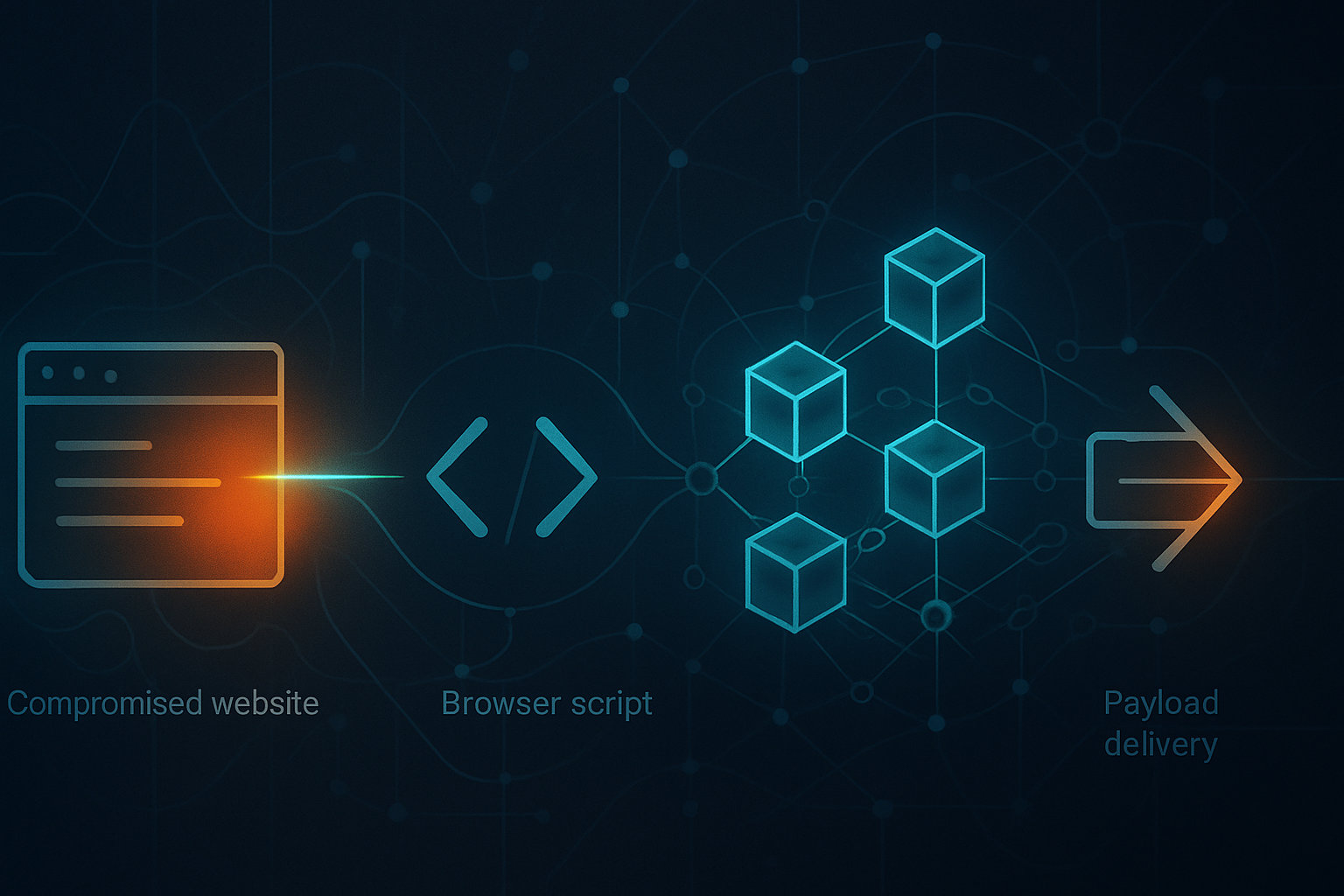
TWCERT/CC describes a common pattern since 2024: attackers compromise vulnerable WordPress sites and inject malicious JavaScript. Visitors are then shown fake system notifications or software-update prompts (ClearFake). If a user interacts, the script queries a BSC smart contract to fetch the attacker’s latest instructions or payload location via EtherHide, and then proceeds to download and deploy the next stage.
This is operationally meaningful for security and infrastructure teams because it crosses traditional boundary lines:
– Web security: compromised CMS platforms become the initial distribution layer.
– Endpoint security: the final payload execution happens on user devices.
– Cloud/network security: the “C2” may be reachable through commodity blockchain RPC paths that are not traditionally treated as high-risk.
Why BSC and eth_call are highlighted
TWCERT/CC notes EtherHide is often deployed on Binance Smart Chain (BSC) and suggests this may be due to ecosystem and API convenience. The advisory specifically calls out the use of the Binance SDK’s eth_call method for smart-contract reads. As described by TWCERT/CC, eth_call does not require gas fees and does not leave an on-chain transaction record, enabling frequent, lower-friction retrieval of instructions—an attractive property for stealthy C2-style workflows.
Defensive implications (as framed by TWCERT/CC)
TWCERT/CC’s recommendations align to the multi-stage nature of the chain:
– Reduce initial web compromise risk (e.g., keep WordPress core and plugins updated; use WAF) to prevent malicious JavaScript injection.
– Rely on endpoint detection and dynamic analysis/sandboxing to catch payload execution and abnormal behavior after user interaction.
– Run ongoing security-awareness training focused on fake updates and deceptive prompts.
– For sensitive environments that must interact with public chains via nodes/RPC, plan allowlisting or other access controls to reduce exposure to malicious on-chain data.
– Security vendors should consider EtherHide-like patterns as an emerging threat source for behavior models and threat intelligence.
Bottom line
TWCERT/CC’s advisory underscores that blockchain is being operationalized not only for fraud but also as resilient C2 plumbing. For global defenders, the key shift is that “C2 disruption” may increasingly require correlating web compromise signals, endpoint behavior, and blockchain/RPC access patterns—rather than relying primarily on domain/IP-based blocking alone.
Event Type: security
Importance: high
Affected Companies
- Binance
- TWCERT/CC
- WordPress
Affected Sectors
- Blockchain
- Cloud Security
- Cybersecurity
- Web Infrastructure
Key Numbers
- TWCERT/CC publication date: 2025-11-27
- When researchers first proposed EtherHide (per TWCERT/CC): 2023-10
- When ClearFake was first observed (per TWCERT/CC): 2023 Q2
- BSC launch year cited by TWCERT/CC: 2020
- TWCERT/CC page views (at time of capture): 12148
Timeline
- Binance Smart Chain (BSC) launched (as cited by TWCERT/CC).
- ClearFake fake-update social-engineering activity first observed (per TWCERT/CC).
- Security researchers first introduced the “EtherHide” technique (per TWCERT/CC).
- Common attack chain: compromise vulnerable WordPress sites → inject malicious JavaScript → show fake update prompt (ClearFake) → query BSC smart contract for payload/commands (EtherHide) → download and run next-stage malware.
- TWCERT/CC publishes advisory on the emerging blockchain C2 threat and defensive considerations.