Answer Brief
Microsoft’s MSRC investigation into Storm-0558 concludes that operational errors likely allowed Microsoft Account (MSA) consumer signing key material to escape a secure token signing environment via a crash-dump/debug workflow, after which the actor (attributed by Microsoft as China-based) likely obtained it by compromising a Microsoft engineer’s corporate account with access to the debugging environment. A separate engineering failure—missing issuer/scope validation when mail systems relied on a common key metadata endpoint—meant a consumer key could be used to forge tokens accepted for enterprise email access. Microsoft says it has since corrected the race condition, improved key-material detection and credential scanning, and updated libraries to automate scope validation.
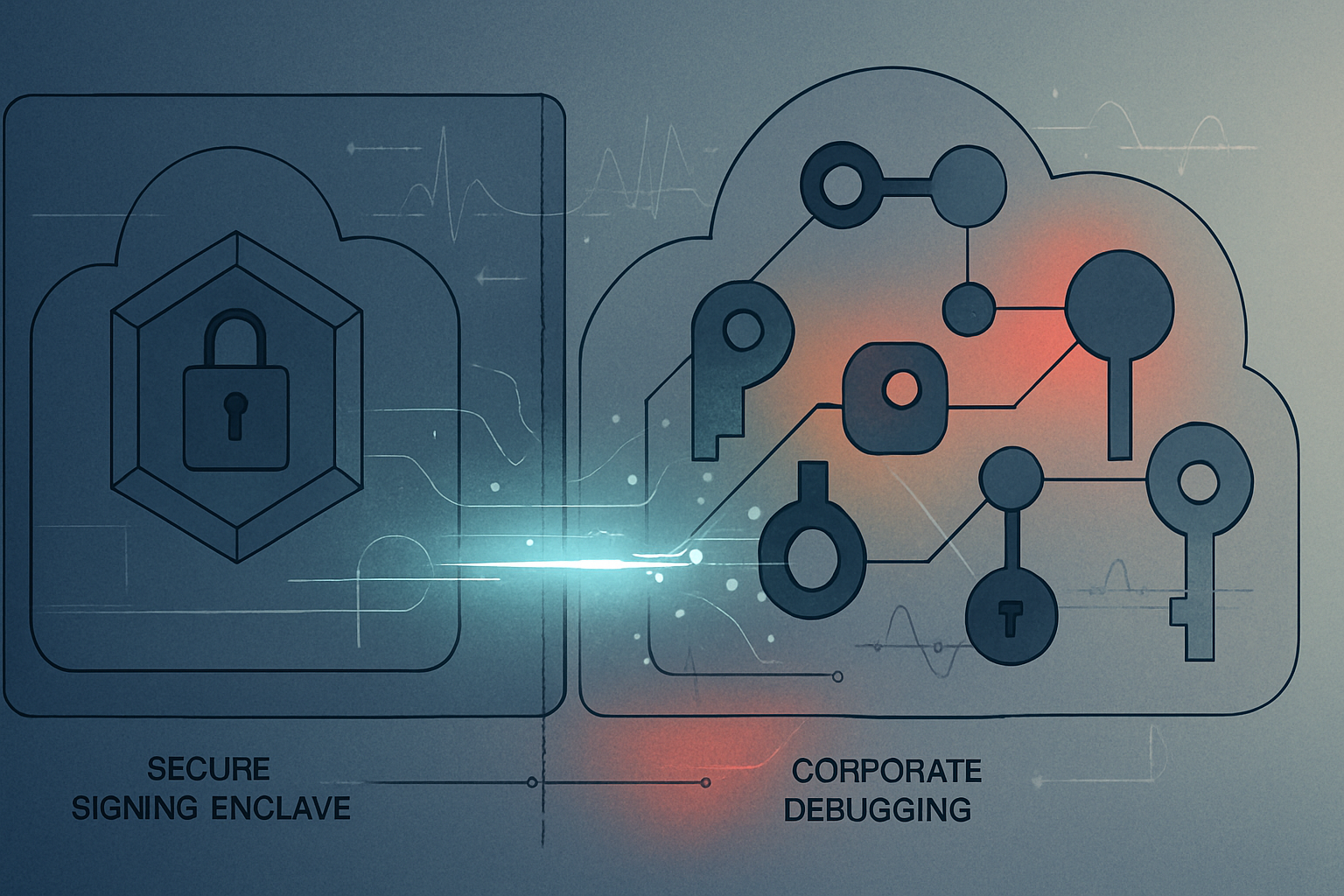
Executive Summary: Microsoft’s MSRC investigation into Storm-0558 concludes that operational errors likely allowed Microsoft Account (MSA) consumer signing key material to escape a secure token signing environment via a crash-dump/debug workflow, after which the actor (attributed by Microsoft as China-based) likely obtained it by compromising a Microsoft engineer’s corporate account with access to the debugging environment. A separate engineering failure—missing issuer/scope validation when mail systems relied on a common key metadata endpoint—meant a consumer key could be used to forge tokens accepted for enterprise email access. Microsoft says it has since corrected the race condition, improved key-material detection and credential scanning, and updated libraries to automate scope validation.
Why It Matters
Microsoft’s write-up is a rare, detailed look at how modern cloud identity failures can occur not just through cryptographic breaks, but through operational pathways (debug artifacts), environment boundary assumptions (production vs. corporate networks), and incomplete validation semantics (scope/issuer checks).
Key takeaways for cloud identity and security teams:
• Debugging pipelines can become key-exfiltration pipelines. Microsoft’s leading hypothesis is that operational errors caused key material to leave a secure signing environment and become accessible in a corporate-network debugging environment, which was then reachable via a compromised engineering account. Even though production environments can be highly restricted, the moment sensitive artifacts are moved for troubleshooting, the threat model shifts to the corporate endpoint and identity plane.
• Detection and retention gaps can limit certainty after the fact. Microsoft notes log retention policies prevented it from producing direct evidence of exfiltration, framing the mechanism as “most probable.” This underscores that post-incident confidence can hinge on long-lived telemetry for high-impact identity assets.
• “Converged” endpoints increase the blast radius of validation mistakes. Microsoft attributes the enterprise impact to two design/implementation realities: (1) a common key metadata publishing endpoint for consumer and enterprise, and (2) mail-system developers incorrectly assuming helper libraries performed complete validation, omitting issuer/scope validation. In effect, a consumer signing key became acceptable for enterprise-mail tokens when validation logic did not enforce the intended trust boundary.
• Library behavior and documentation are security controls. Microsoft says it clarified documentation and released enhanced libraries to automate scope validation. The incident illustrates how security invariants can fail when they rely on every downstream service team implementing subtle validation rules consistently.
Why this matters beyond Microsoft: many enterprises are consolidating identity infrastructure, metadata endpoints, and validation libraries across multiple account types, tenants, and cloud workloads. This postmortem shows how cross-domain key reuse (or shared metadata) plus incomplete semantic validation can turn a single key compromise into an enterprise-access pathway, even if cryptography remains sound.
Microsoft-reported remediations include fixing the race condition, enhancing prevention/detection/response for key material in crash dumps, improving credential scanning for key presence in debugging environments, and updating authentication libraries to automate key scope validation. Microsoft states the March 2024 addendum does not change previously shared customer guidance and that no additional customer action is required.
Event Type: security
Importance: high
Affected Companies
- Microsoft
Affected Sectors
- Cloud Identity
- Cloud Security
- Email Security
- Enterprise SaaS
- Incident Response
Key Numbers
- Common key metadata publishing endpoint introduced: September 2018
- Crash involving consumer signing system (per Microsoft): April 2021
- Mail systems updated to use common metadata endpoint: 2022
- Microsoft preliminary investigation published: July 11, 2023
- Major technical investigations announced complete: September 6, 2023
- Microsoft addendum/update to this post: March 12, 2024
Timeline
- Microsoft introduces a common key metadata publishing endpoint intended to support apps spanning consumer and enterprise contexts (per Microsoft).
- A consumer signing system crash produces a crash dump; Microsoft says a race condition allowed key material to be present and that it was later moved into a corporate-network debugging environment.
- Mail systems adopt the common metadata endpoint; Microsoft says required issuer/scope validation was not added, enabling acceptance of enterprise-mail requests signed with the consumer key.
- Microsoft publishes preliminary findings on Storm-0558’s use of an acquired MSA consumer signing key to forge tokens for OWA and Outlook.com access.
- Microsoft states major technical investigations into key acquisition are complete and releases findings.
- Microsoft issues an update clarifying uncertainties (e.g., no crash dump containing the impacted key has been found) and tightening statements about debugging processes and cred-scanning limitations.